38 security labels access control
Introduction to column-level access control | BigQuery ... 2 days ago · Using BigQuery column-level access control, you can create policies that check, at query time, whether a user has proper access. For example, a policy can enforce access checks such as: You must be in group:high-access to see the columns containing TYPE_SSN. To enhance column-level access control, you can optionally use dynamic data masking ... Multi-tenant access for Managed Security Service Providers Jul 20, 2020 · Turning on role-based access control will cause users with read-only permissions (for example, users assigned to Azure AD Security reader role) to lose access until they are assigned to a role. Users with admin permissions are automatically assigned the default built-in Microsoft Defender ATP global administrator role with full permissions.
Microsoft 365 guidance for security & compliance - Service ... Sep 19, 2022 · To benefit from the Conditional Access App Control capabilities in Defender for Cloud Apps, users must also be licensed for Azure Active Directory P1, which is included in Enterprise Mobility + Security F1/F3/E3/A3/G3, Enterprise Mobility + Security E5, Microsoft 365 E3/A3/G3, Microsoft 365 E5/A5/G5, and Microsoft 365 E5/A5/G5/F5 Security and ...
Security labels access control
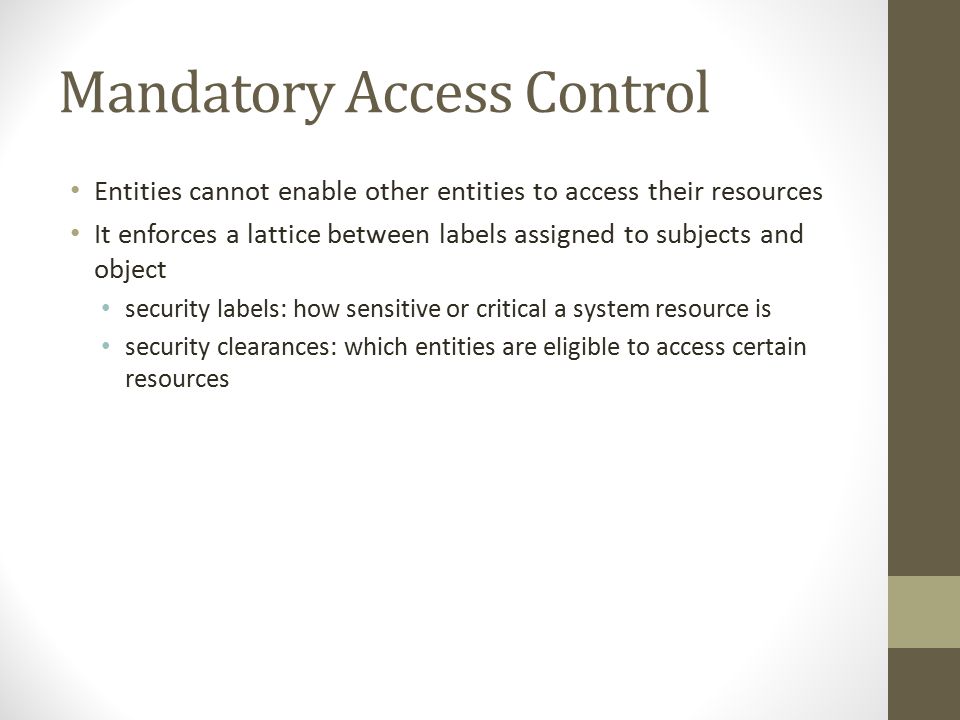
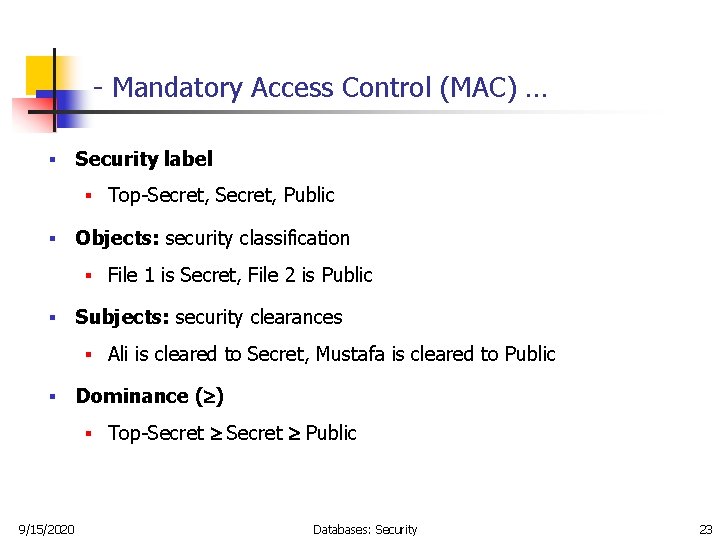
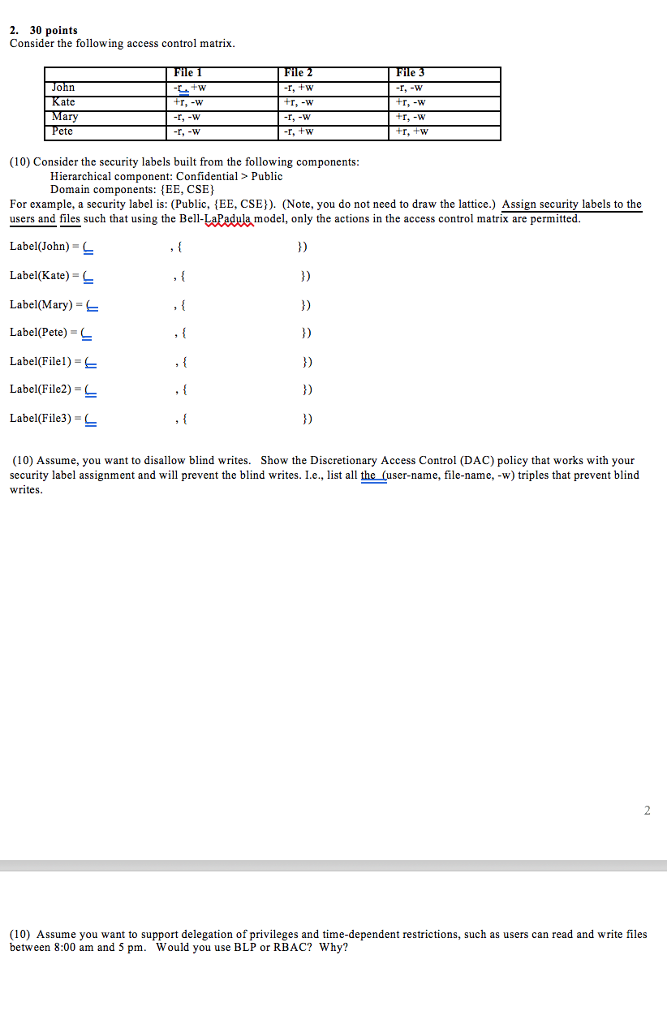
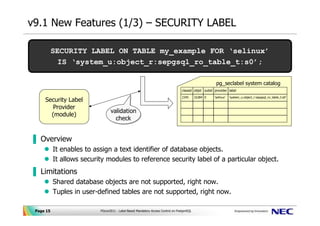
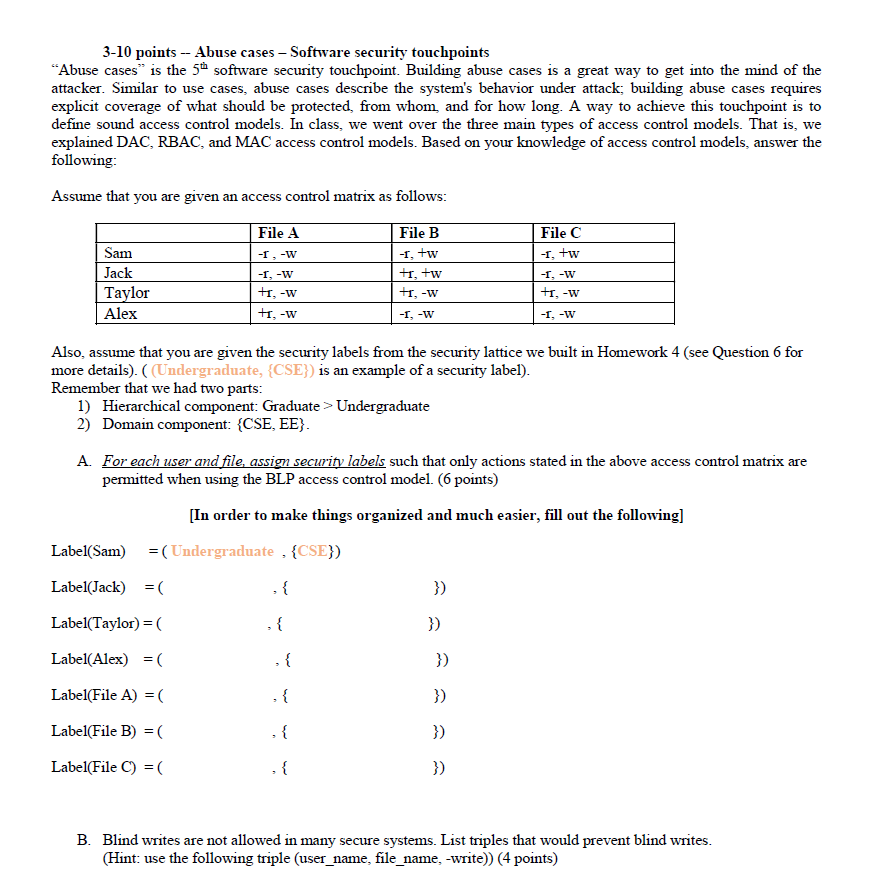
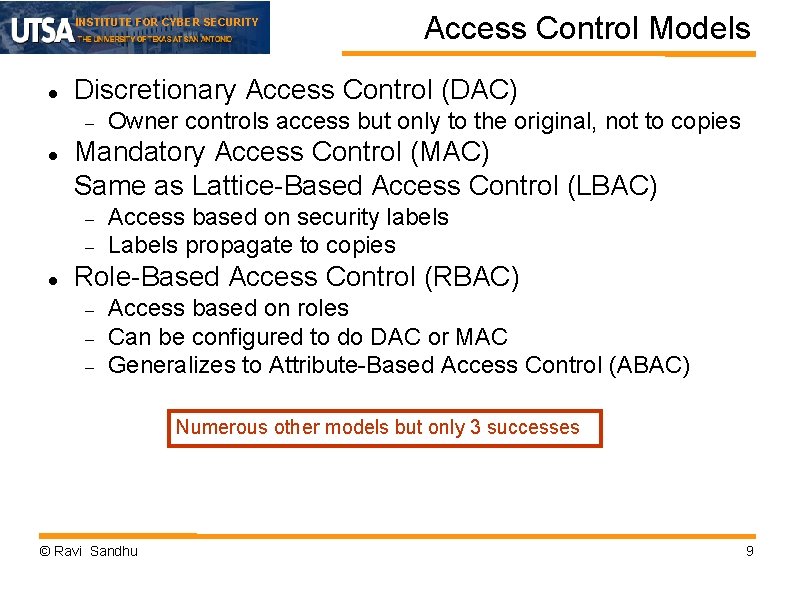
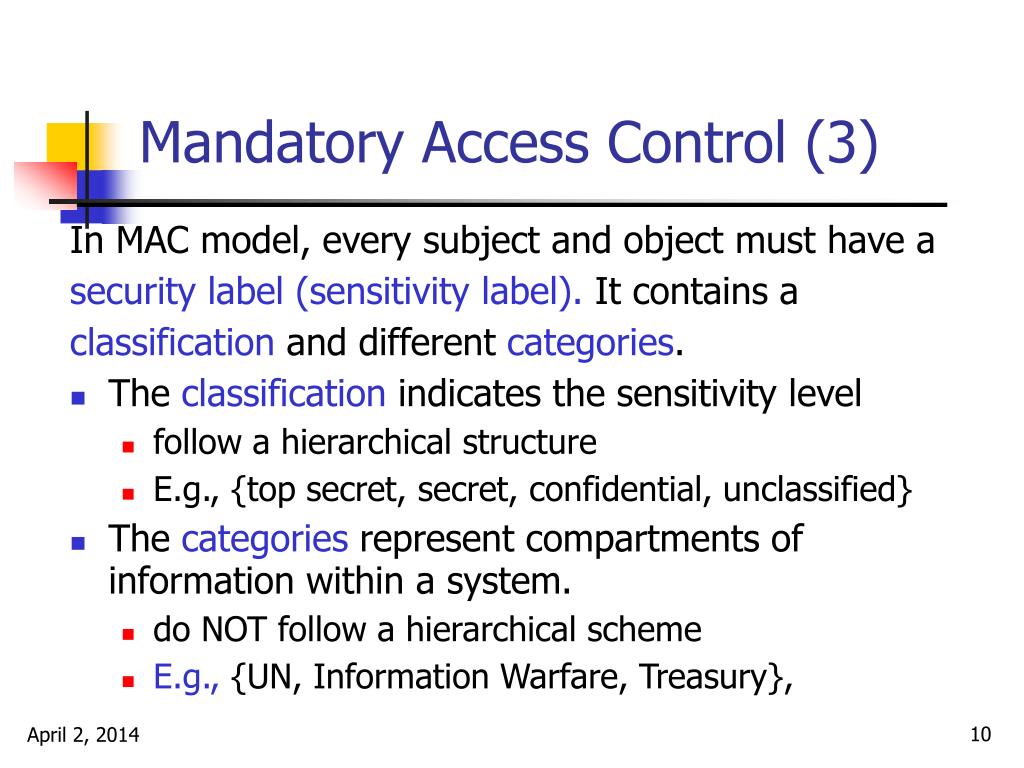
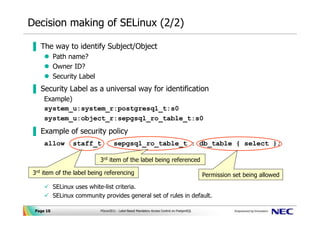
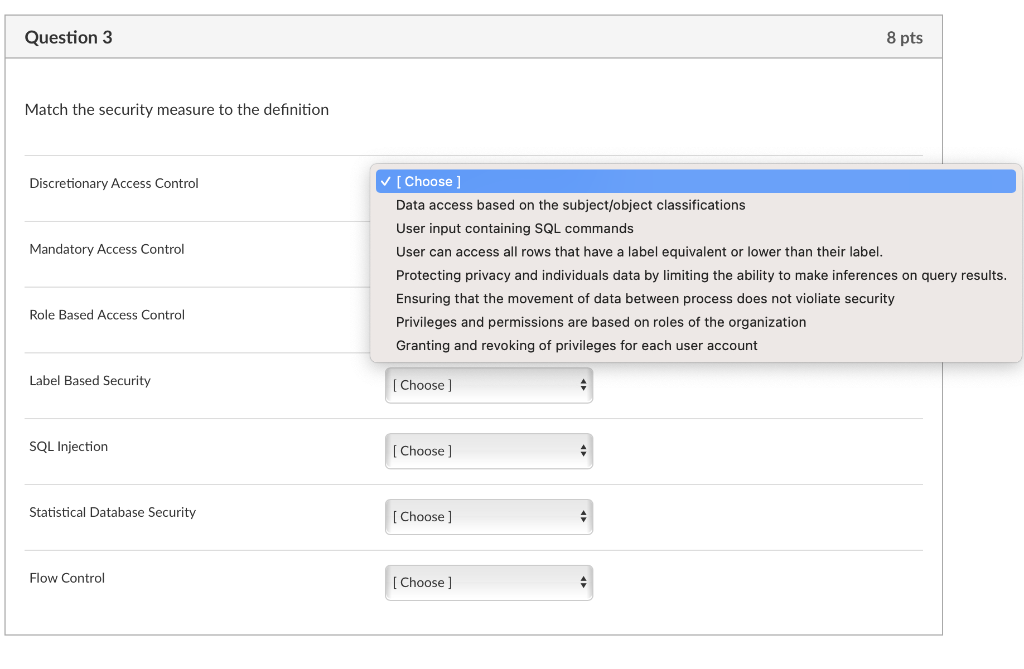
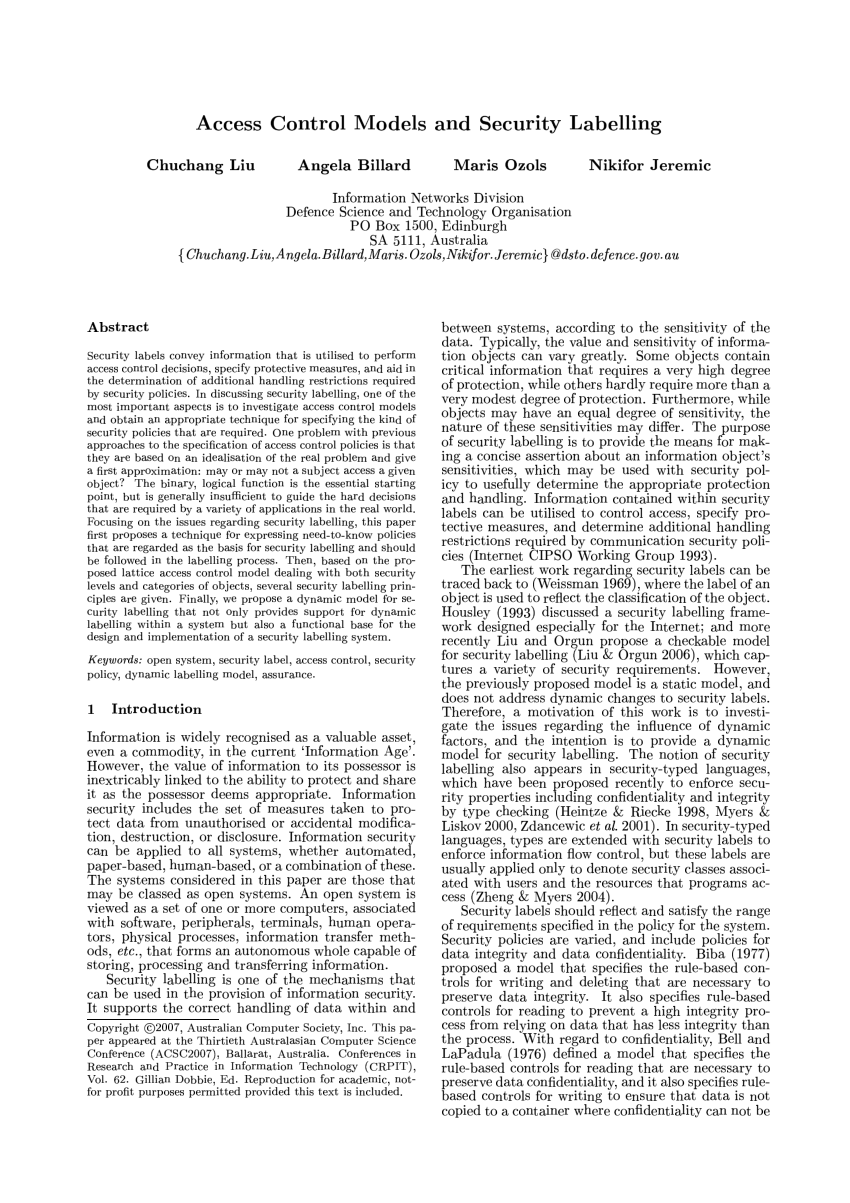
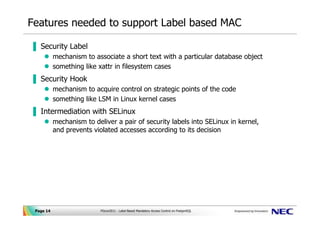
Security - FHIR v4.3.0 - Health Level Seven International Two of the classic Access Control models are: Role-Based Access Control (RBAC), and Attribute-Based Access Control (ABAC). In Role-Based Access Control (RBAC), permissions are operations on an object that a user wishes to access. Permissions are grouped into roles. A role characterizes the functions a user can perform. Roles are assigned to users. SPARQL 1.1 Query Language - W3 1 Introduction. RDF is a directed, labeled graph data format for representing information in the Web. RDF is often used to represent, among other things, personal information, social networks, metadata about digital artifacts, as well as to provide a means of integration over disparate sources of information. Mandatory Access Control: How does it work? - IONOS Oct 14, 2020 · There are a number of options available for implementing and maintaining access control, including Mandatory Access Control. This model is also used in the political and military branches, which require tamper-proof protection of data. Keep reading to find out how this rule-based access control works and what its pros and cons are.
Security labels access control. Access control for folders with IAM | Resource Manager ... Sep 28, 2022 · IAM lets you adopt the security principle of least privilege, so you grant only the necessary access to your resources. IAM lets you control who (users) has what access (roles) to which resources by setting IAM policies. IAM policies grant specific role(s) to a user giving the user certain permissions. Mandatory Access Control: How does it work? - IONOS Oct 14, 2020 · There are a number of options available for implementing and maintaining access control, including Mandatory Access Control. This model is also used in the political and military branches, which require tamper-proof protection of data. Keep reading to find out how this rule-based access control works and what its pros and cons are. SPARQL 1.1 Query Language - W3 1 Introduction. RDF is a directed, labeled graph data format for representing information in the Web. RDF is often used to represent, among other things, personal information, social networks, metadata about digital artifacts, as well as to provide a means of integration over disparate sources of information. Security - FHIR v4.3.0 - Health Level Seven International Two of the classic Access Control models are: Role-Based Access Control (RBAC), and Attribute-Based Access Control (ABAC). In Role-Based Access Control (RBAC), permissions are operations on an object that a user wishes to access. Permissions are grouped into roles. A role characterizes the functions a user can perform. Roles are assigned to users.
Long Range Access Control UHF RFID Car Windshield Sticker Label Tag for UHF Reader Vehicle Tracking Management

Keychain Sticker Card Label Key IC Keychain Access Control EM Keychain Token Portal Reader 13.56MHZ RFID Multi-color Optional
Access Control Card Customized Printing Rfid Paper Roll Label Rfid Security Label For Acess Control System - Buy Paper Roll Smart Uhf Sticker Tag Label Long Range Rfid Sticker - Buy Rfid Sticker Long ...











![PDF] A System for Supporting The Cyber Security Control of ...](https://d3i71xaburhd42.cloudfront.net/e24f299c73998f565a63fa1258a15c55ab10c816/2-Table1-1.png)
!['Mandatory Access Control Essentials with SELinux': Costas Senekkis, ICSI [CRESTCon 2019]](https://i.ytimg.com/vi/h4eG8y53D9Q/maxresdefault.jpg)

Post a Comment for "38 security labels access control"